3 min read
Conducting a third-party audit
Conducting a third-party audit involves evaluating an organization’s processes, systems, or practices to assess compliance with national standards,...
%20-%202024-12-17T182255.264.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-17T182255.264.jpg)
3 min read
Conducting a third-party audit involves evaluating an organization’s processes, systems, or practices to assess compliance with national standards,...
%20-%202024-12-17T124136.948.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-17T124136.948.jpg)
3 min read
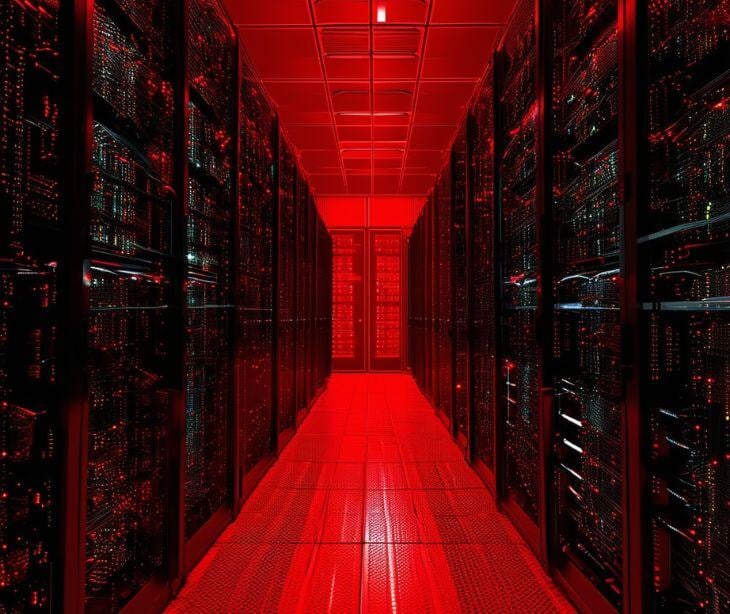
With over 328 million terabytes of data generated daily, cyber threats are rising as criminals seek to exploit this valuable resource. Today, secure...
1 min read
The attack resulted in the state shutting down its online benefits systems.
%20-%202024-12-16T183903.440.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-16T183903.440.jpg)
2 min read
Robust security practices refer to a comprehensive set of actions, tools, and strategies designed to protect systems, networks, and data from...
%20-%202024-12-16T063004.725.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-16T063004.725.jpg)
2 min read
Cybercriminals use stolen data for many malicious purposes, like financial gain, extortion, and more.

3 min read
Russia frequently appears in discussions about cyber attacks, and for good reason. The country’s geopolitical climate, legal policies, and thriving...
%20-%202024-12-11T192642.729-1.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-11T192642.729-1.jpg)
2 min read
Strong security practices and methodologies, such as email authentication, are advisable to protect organizations from cyber threats. These are...
%20-%202024-12-11T190853.293.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-11T190853.293.jpg)
2 min read
HIPAA audit controls refer to the mechanisms and policies covered entities and business associates implement to track and monitor access to...
%20-%202024-12-11T185706.590.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-11T185706.590.jpg)
2 min read
Access control ensures that only authorized users can interact with systems and data, while audit control provides visibility and accountability...

2 min read
The US Food and Drug Administration (FDA) recently called on blood suppliers to increase their cybersecurity to safeguard the safety and integrity of...
%20-%202024-12-09T062933.468.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-09T062933.468.jpg)
1 min read
Technological risks are the vulnerabilities arising from digital infrastructure. Meanwhile, physical risks are threats that could lead to physical...
%20-%202024-12-09T061024.387.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-09T061024.387.jpg)
2 min read
Organizations must secure any vulnerabilities in central storage devices. Security requirements may depend on the device and the organization, as...
%20-%202024-12-06T133437.110.jpg?width=730&height=614&name=Paubox%20template%20(730%20x%20614%20px)%20-%202024-12-06T133437.110.jpg)
2 min read
Cost-benefit analyses (CBAs) are rooted in economic evaluation, assigning monetary values to both costs and benefits. It can be applied to risk...